Resources
A collection of Anvilogic blogs, webinars, and solution deep dives to explore our products, use cases, and integrations.
.avif)
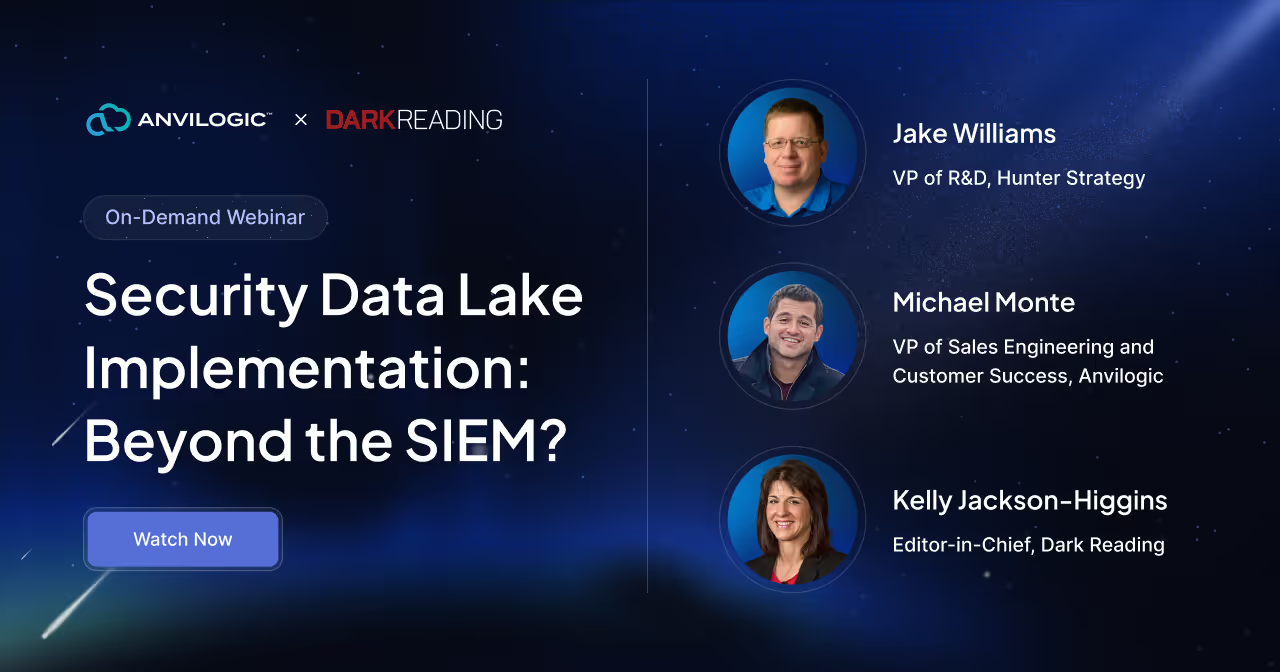
On-Demand Webinar
Security Data Lake Implementation: Beyond the SIEM?
All Resources

Executive Overview
Rethinking UEBA with Anvilogic's Behavioral-Based Approach

Executive Overview
Anvilogic for Databricks: AI-Powered Threat Detection In Your Lakehouse

Solution Brief
An AI Assistant that understands the SOC

Solution Brief
Anvilogic AI Insights: AI-Powered Tuning, Hunting & Detection Health

Executive Overview
The Agnostic Advantage A New Era of SIEM Flexibility

Executive Overview
Build Detections You Want, Where You Want with Anvilogic
Watch
.png)
On-Demand Webinar
Unlocking Security Optimization Amongst a Multi-Data Platform Strategy
Webinar

On-Demand Webinar
Revolutionizing the SIEM: How Data Lakes are at the Center of a Modern Security Architecture
Webinar

On-Demand Webinar
Strategies for Decoupling Your Security Analytics and Adopting a Modern Security Data Lake
Webinar

Post Splunk: Your roadmap to adopting a cost-effective cloud-native security data lake at your own pace
Webinar

Demos
Stop Alert Fatigue: Understanding the Importance of Sequence-Based Detections

Demos
Exploring New Capabilities for Snowflake Users with Anvilogic
Podcast

Does the SOC have a Memory Problem?? A better approach to your field notes feat. K.C Yerrid
.png)
The New Definition of Visibility & the Evolving Role of IOCs: Detection Engineering Through a UFO Lens with David Burkett
The SOC Then vs Now...a 'Possible Travel' Season 2 Special Feat. Matt Konwiser & Chris Liccardi
.png)
Cool Story, Bro: Making Detection Engineering Matter Up the Chain

To AI SOC or not to AI SOC? Feat. Dennis Chow
.png)
Spencer Pratt on Agentic RAGs + Chicago Reccs for Newbies
Read

Event
GBI: Los Angeles, CA
.avif)
Event
Gartner Security & Risk Management Summit
.png)
Event
Minneapolis Forum

Event
GBI: Toronto, Canada

Event
IANS: Dallas, TX


Blog
A Technical Guide to Automating SOC Operations with Anvilogic Blueprints


Build Detections You Want, Where You Want







