Resources
A collection of Anvilogic blogs, webinars, and solution deep dives to explore our products, use cases, and integrations.
.avif)
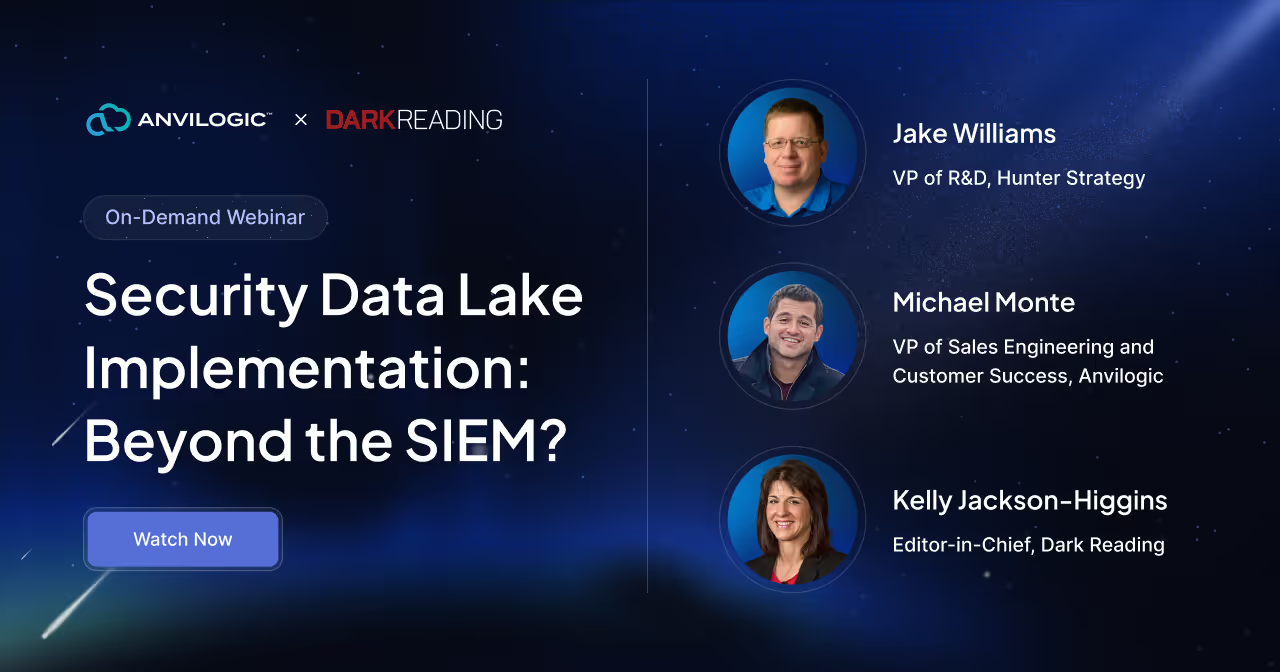
On-Demand Webinar
Security Data Lake Implementation: Beyond the SIEM?
All Resources

Event
GBI: Los Angeles, CA
.avif)
Event
Gartner Security & Risk Management Summit
.png)
Event
Minneapolis Forum

Event
GBI: Toronto, Canada

Event
IANS: Dallas, TX


Blog
A Technical Guide to Automating SOC Operations with Anvilogic Blueprints
Watch
-min.png)
Build Your Security Operations for the Long Haul Feat. Rubrik
Webinar
-min.png)
Better Detection, Hunting & Triage With Anvilogic For Splunk
Webinar
-min.png)
Unlock Your SOC: Move from Tactical to Strategic Feat. Twitter
Webinar
-min.png)
Ensure Your SOC is Living Up to Its Potential Feat. Trace3
Webinar
.png)
Day in a Life of a SOC Team With Toast & Anvilogic
Webinar
Podcast

5 Bitter Pills to Swallow RE: Agentic AI

5 Signs You’re Overengineering Your Detection Logic

Hack my S3: We Simulated the Breach — Here's What We Learned

The AI Series: Inside URL Guardian—An LLM Built for Detection

The UEBA Illusion: Why Traditional UEBA Falls Short

Machine Learning-Powered Threat Hunting feat. Sydney Marrone
Read

Event
GBI: Los Angeles, CA
.avif)
Event
Gartner Security & Risk Management Summit
.png)
Event
Minneapolis Forum

Event
GBI: Toronto, Canada

Event
IANS: Dallas, TX


Blog
A Technical Guide to Automating SOC Operations with Anvilogic Blueprints


Build Detections You Want, Where You Want







